Blog Posts
This blog post details exploitation of arbitrary deserialization for the Ruby programming language and releases the first public universal gadget chain to achieve arbitrary command execution for Ruby 2.x.
Reviewing the security of the Fuze card device revealed no trust boundary between the card and the connecting device, which allowed complete access to the Fuze card's settings and stored credit-card information.
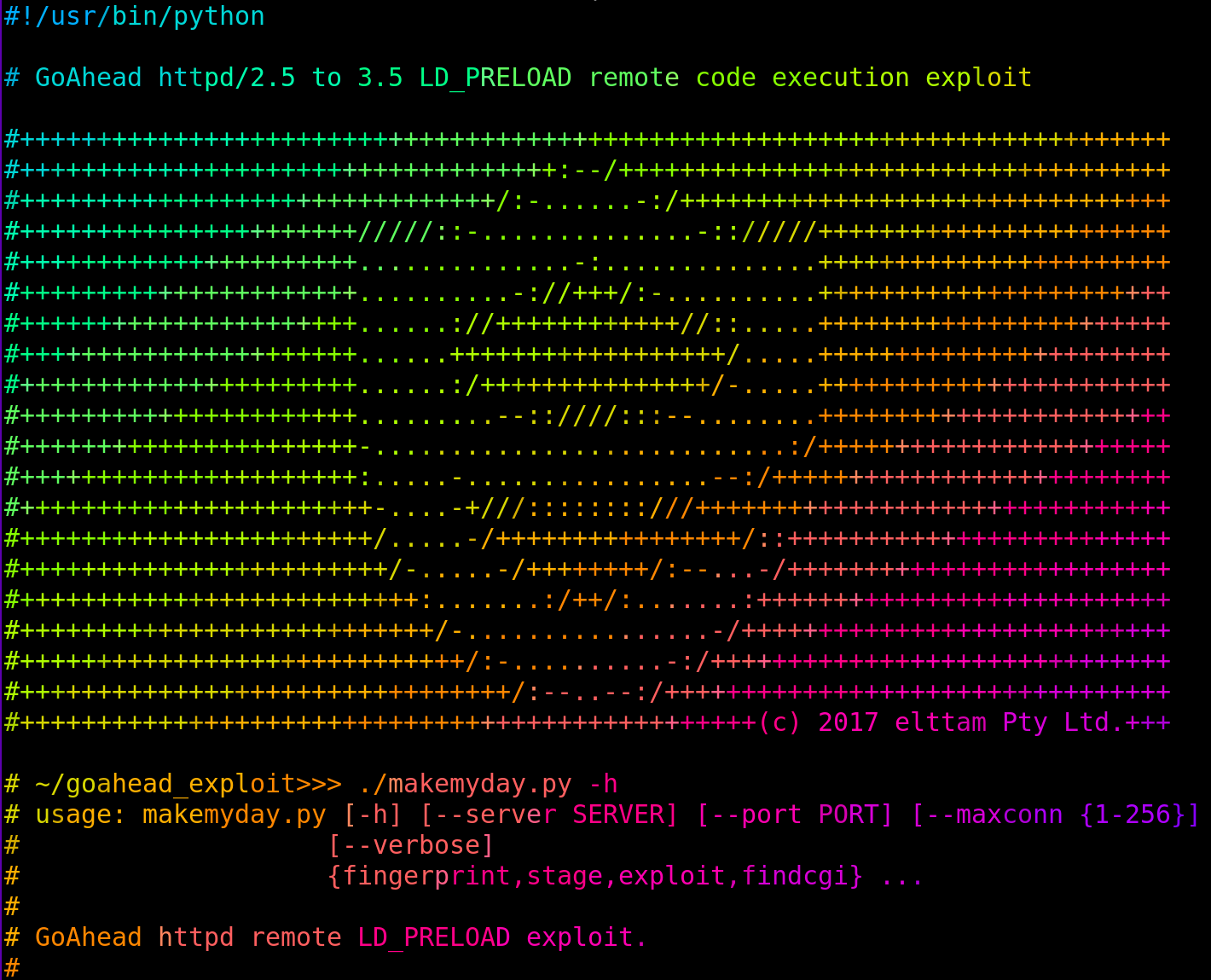
Analysing a vulnerability in all versions of the GoAhead web server < 3.6.5 that allowed for reliable remote code execution via LD_PRELOAD injection.
How to use Kubler to build hardened, minimalistic, Docker Images from scratch for better security