Resources
Research, experimentation, and continuous improvement are fundamental to how we operate at elttam. Our consultants spend a significant amount of time exploring new technologies, building tooling, analysing vulnerabilities, and turning interesting problems encountered in the field into deeper technical investigations.
This section brings together that work - from detailed research posts and vulnerability disclosures to tools, publications, and updates from the team. By sharing what we learn, we aim to contribute back to the security community while pushing our own knowledge and capabilities forward.
Thank you! Your submission has been received!
Oops! Something went wrong while submitting the form.
In the News
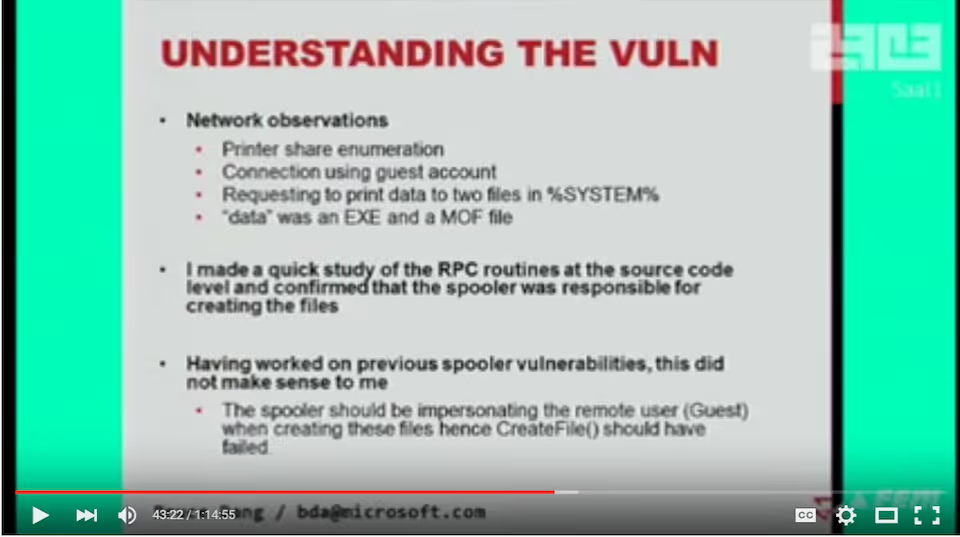
What all the fuss is about